From the Microsoft Azure documentation, the Azure Key Vault service is:
Cloud applications and services use cryptographic keys and secrets to help keep information secure. Azure Key Vault safeguards these keys and secrets. When you use Key Vault, you can encrypt authentication keys, storage account keys, data encryption keys, .pfx files, and passwords by using keys that are protected by hardware security modules (HSMs).
This service is perfect for saving all kinds of information in a secure manner: authentication keys to connect to a database server, SSL certificate files, and of course, passwords… or as Azure Key Vault names them, secrets.
Recently, Microsoft released a connector to use this service (still in preview) so building a Power App to manage these secrets is a match made in heaven.
Building our app
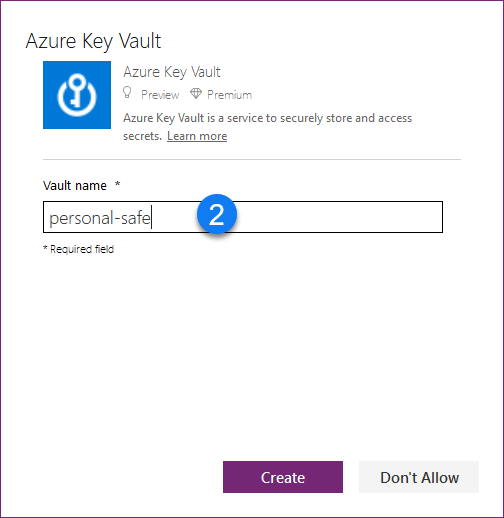
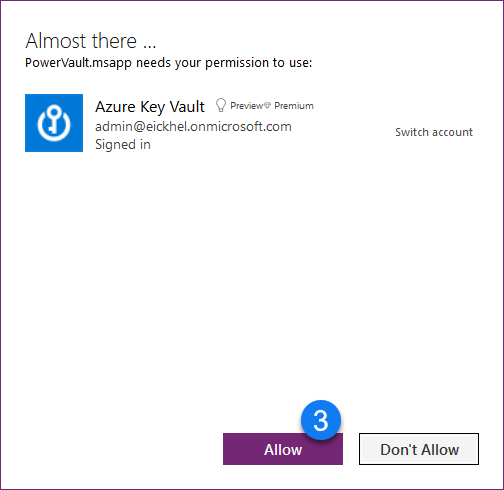
The first thing to do is to configure the connector:
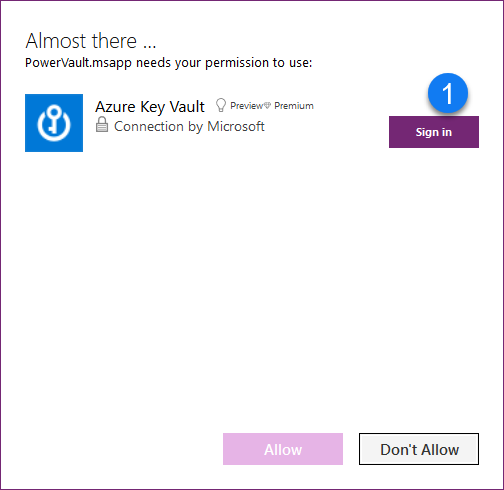
- Sign-in with the account which has access to the Key Vault service
- Specify the vault name
- Allow the connection
As you can see, it’s a very simple task. Once we’ve set it up, we can use the methods available to handle the secrets:
- ListSecrets
- GetSecret
A little bells and whistles and we can get something like this:
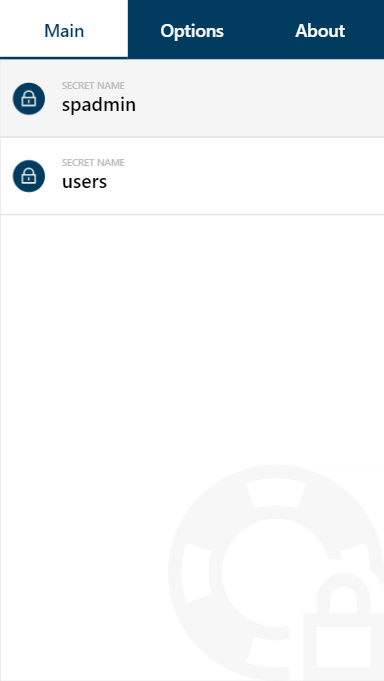
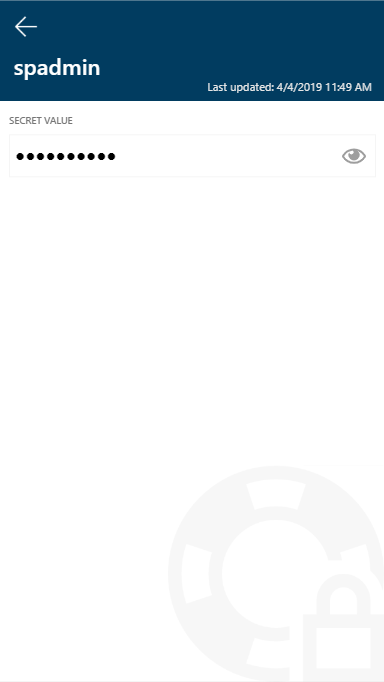
A gallery which holds the list of secrets, a detail screen to display the actual secret value and finally the options and about screen. Look for the download link at the end of the post.
Enhanced Power Apps functionality
But of course, I couldn’t resist including the new Power Apps capabilities when working with responsive layouts (even further).
This allow us to have the building blocks to create one Power App for all devices! forget about having one for mobile devices and another for desktops. With some low-code bits and pieces, we can handle these layouts to our hearts content.
As you can see, we can even play with having a reading pane that only appears when it has the proper dimension to be displayed correctly. This can also be disabled through the app options.
Further improvements
In this release, we can only consume the secrets from Azure Key Vault, we can’t make any changes to it. This is a current limitation from the connector. Keep in mind that it is in a preview stage.
To overcome this, in my next post I will describe how to create a custom connector that will give us more functionality and flexibility in order to have a proper password manager.
Where can I get PowerVault?
As usual, you can get all my apps from my GitHub repository:
https://github.com/Eickhel/PowerApps-samples
See you in the next PowerVault post, and don’t forget, never stop learning!




Just letting you know the links to the repo are broken in this article. Looks interesting. What’s the reason for removing the source in the repo? Have you found a gaping flaw or found something better?