Security is a big concern among organizations around the globe. For this reason, Microsoft provides all sorts of security measures that companies adopt to protect their services.
I was recently deploying a Power Automate solution for a customer when I came across a particular situation. The Cloud flow needed to get some information from an in-house API secured using an IP address allow list.
The issue
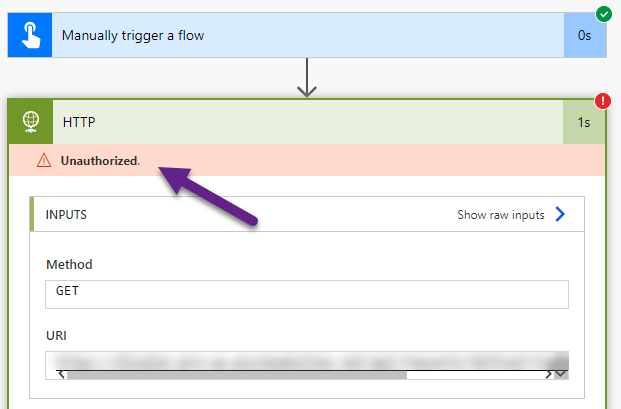
I’ve created an Instant cloud flow with an HTTP request to perform the task and, upon execution, I’ve got the expected Unauthorized error message.
After getting this, I’ve resorted to the Microsoft Docs documentation regarding the limits and configurations to get the list of IP addresses of the environment’s region. With the help of PowerShell, we added all the IP addresses of Europe but the cloud flow kept failing. We also tried adding IP addresses from other regions without any luck. Later, I’ve remembered that Power Automate is a low-code version of Logic Apps, maybe is using an IP address from this service?
I didn’t want to keep trying all the IP addresses from Power Automate or Logic Apps. I needed to find which IP address my flow was using, so then I could find which region list I needed to include in the allow list.
The solution
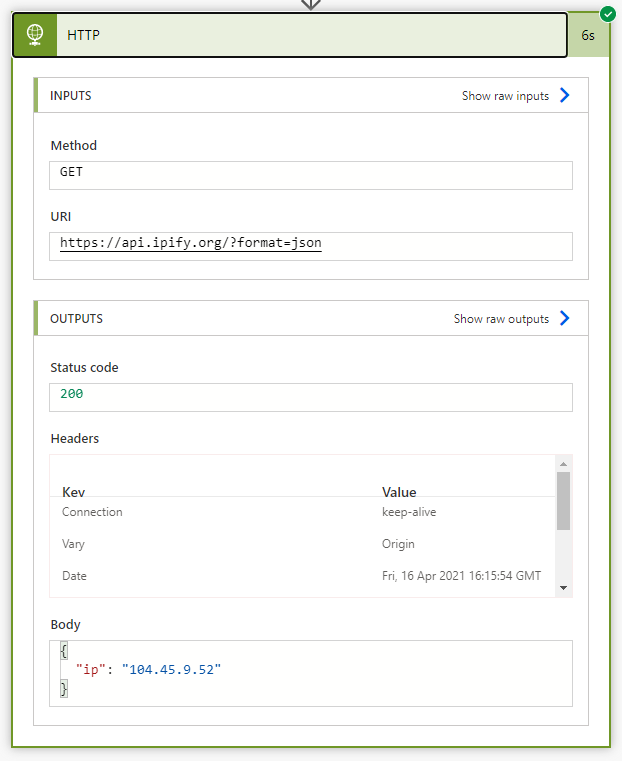
After some research, I’ve found a third-party discovery service called ipfy API which gives you the IP address from which the request is calling, Perfect! 😊
Using the same HTTP action, I’ve sent a request to this service using this URI:
https://api.ipify.org/?format=jsonAnd gotcha!
If you try to find this IP address from the Power Automate documentation, you won’t find it in any region. This is when I’ve tried the list of Azure IP Ranges and Service Tags of the Public Cloud. You can use this link to get this in a JSON Format.
The IP address appears in this list as seen in the following image:
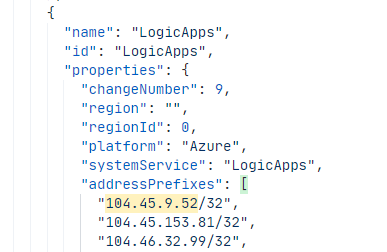
After adding the list of addresses from this region, the in-house API responded successfully 👏🏻👏🏻👏🏻
I hope you find this information helpful when configuring security when using Power Automate.
Never stop learning!




Thank you!
I had my security team whitelist the IP range’s provided by Microsoft for Flow (Power Automate), but clearly Flow is using the Logic App IP ranges. Again, thank you!
Thanks!
Seriously.. your approach helped me to resolve the issue. Thanks a lot!!!
Glad it helped 😊
Did you whitelist the whole IP Range? or just the returned one?
Will the IP of the flow in the specific environment be static? Any clues on this aspect?
This resolved my issue. I have been struggling for last 4-5 hours. Thanks a lot
Hey!
thanks for the help.
But I have a doubt, does the IP address once returned remains static?
Or it gets changed after some interval?
Hey Rishab,
It gets changed after an interval. I don’t know this interval, but is not that random.
Hello, thanks for your info, it’s really good. I whitelisting all the ips but it didn’t work. If I enable access without restriction works perfect. I search in the blob logs, but i didn’t find the IP that the flow shows. Any advice ?